How Silent Shard is Transforming Authentication Support for Crypto Wallets and Exchanges?
At SL, We are removing all excuses by enterprises and communities for not adopting secure ways of signatures and authentication through a unique fusion of multi-party computation (MPC) based cryptography and signal processing based layer of proofs.

Written by
Jay Prakash
Insights
Jun 20, 2022

SHARE
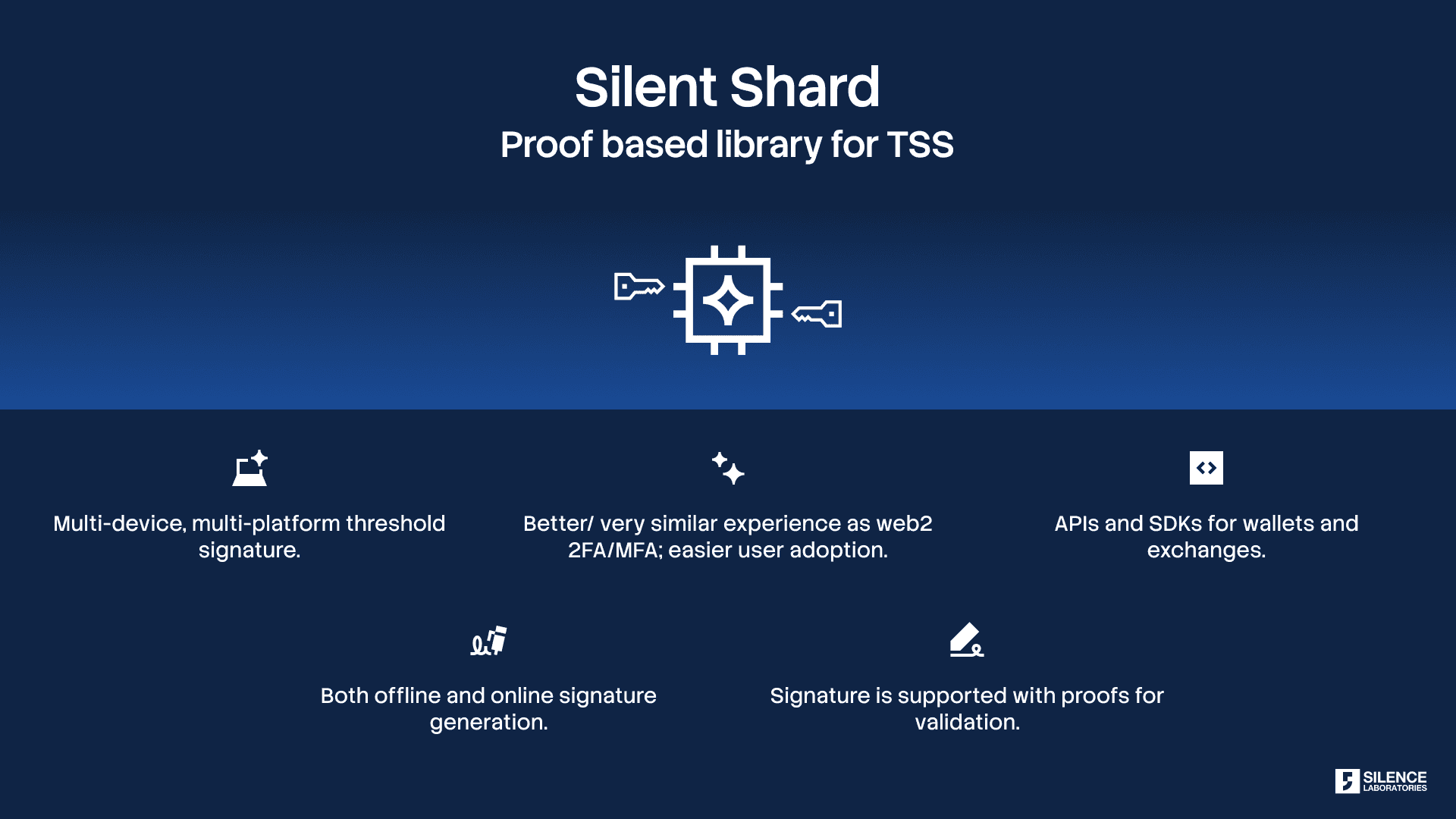
What is Silent Shard?
Silent Shard aims to be the de-facto set of SDKs and APIs for helping enterprises in adopting decentralized and proof-based authentication flows.Silent Shard is the go-to library for threshold signature adoption and supports the inclusion of usable, secure, and truly decentralized signature schemes by digital wallets, exchanges, and login services for Web3/Web2. Web3 has a major difference, when compared to web2, wherein proving possession of the private keys is the only way to verify association/access/claim for an account. In order to protect such systems, Silent Shard derives its name from the concept of sharding (splitting) private keys into portions such that a single point of failure (theft of private keys as a whole) is ruled out.
What are the areas of concern? And why do Crypto Wallets and Exchanges need special attention?
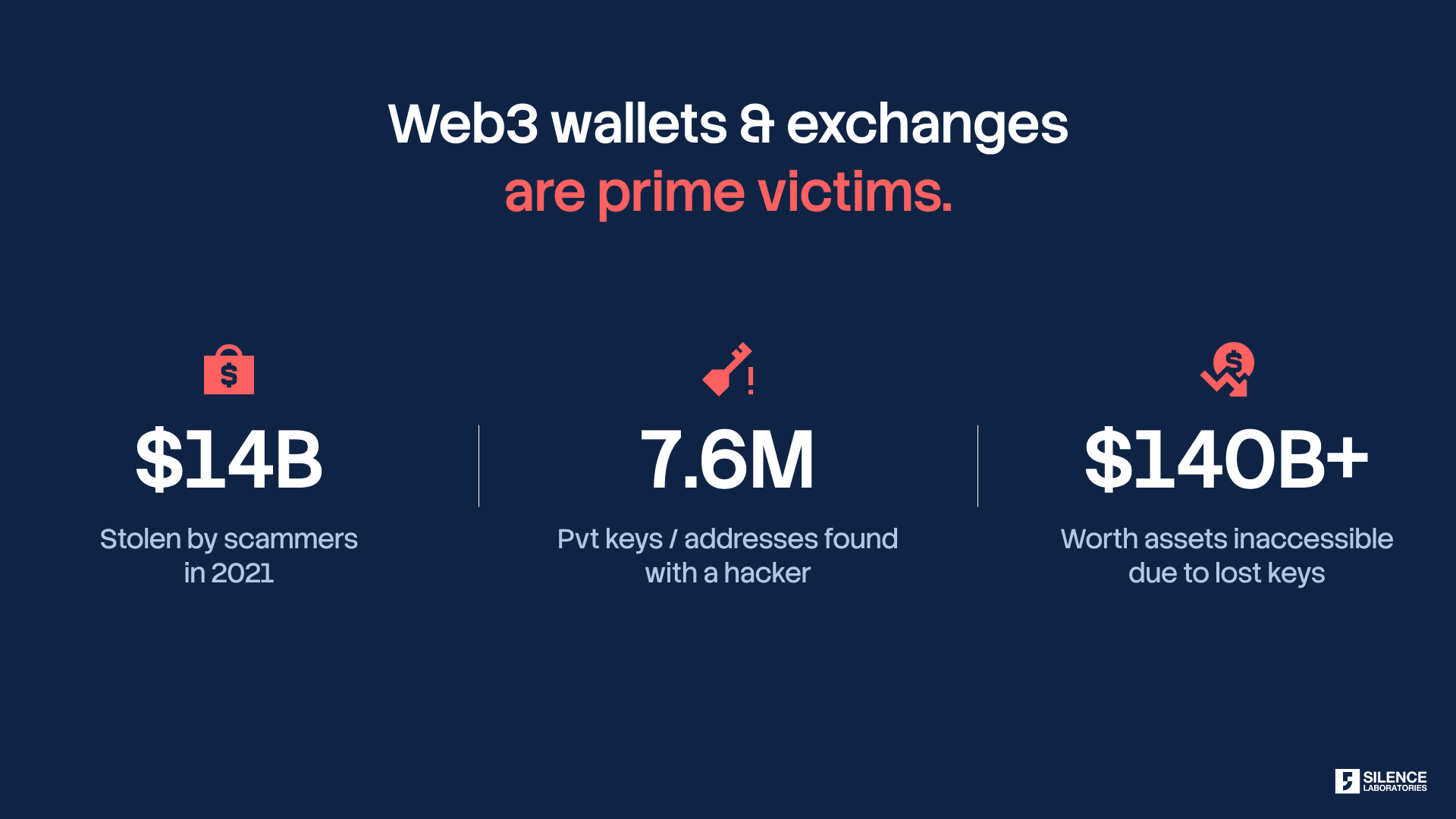
“The Banks of the Web2 world have undo buttons. Web3, blockchain-based applications, do not support that luxury due to their inherent nature.” Crypto wallets are usually associated with a public and a private key pair. The assets are stored on the blockchain where they are attached to a public address. These addresses are unique and used by the sender to transfer tokens to the expected receiver. Users can transact with the wallet only if they can prove the ownership of a private key. Wallets and exchanges have been under the scanner of theft for a while now, and the scale and the nature of compromises have been growing even more sophisticated over the past five years.
Cyber attacks against cryptocurrency exchanges are on the rise. Last month, BTC-Alpha confirmed it was the victim of a ransomware attack. Though BTC-Alpha founder Vitalii Bodnar said no hashed passwords were compromised and users’ balances were not impacted, some users cited issues with logging in and not being able to withdraw funds [7]. Group-IB, an international company that specializes in preventing cyber attacks, has estimated that cryptocurrency exchanges suffered a gross loss of $882 million due to targeted attacks in 2017 + in the first three quarters of 2018, alone. According to Group-IB experts, at least 14 crypto exchanges were hacked.
Security concerns with the wallets and exchanges are critical problems and have quantifiably contributed to the loss of nearly 20% of all Bitcoin in circulation.
Associated vulnerabilities of current Authentication mechanisms:
Wallets and Exchanges are facing severe theft and attacks due to unpatched holes in user experience and levels of security:
Issues with Key Management and Signature Processes:
Theft of Private Keys/Seed Phrases: Private keys/seed phrases are stolen or phished through different mechanisms which keep evolving in sophistication.
Hackers use the following techniques to access the private keys:
a) Phishing Attacks: Hackers use cloned websites similar to original websites to deceive the user and mislead them to enter the private key of their crypto wallets. For example, Coinbase.co instead of Coinbase.com. Once hackers get this information, they can use it to access the user’s real crypto wallet and steal money from their account. This has been a common attack vector in MetaMask in the past.
b) Infusing Malwares in User’s Device: Hackers use pre-programmed malware to detect private keys stored on the user’s device and swap them for a wallet owned by hackers. After accessing the private key, hackers can transfer the funds to unintended addresses and it would never be undone from the user’s end.
Examples of attacks related to private keys/seeds
EasyFi — $80 million stolen in April 2021 [2]
The Polygon (formerly MATIC) network saw $6 million in stablecoins and ~$53 million in $EASY tokens taken without any complications when the mnemonic keys for EasyFi fell into the wrong hands. Showing that targeting a person works just as well as targeting a system vulnerability, a hacker targeted the founder’s computing device to get his admin keys and transfer funds to himself. The initial loss was $6 million of stablecoins and $120 million worth of $EASY, the native token of the EasyFi project.
Dego Attack 2022 [3]
~$10M taken across three chains from Dego and their strategic partner Cocos-BCX. Investigation revealed that it was just because of the compromise of private keys.
Vulcan Forged Attack 2021 [4]
Hackers helped themselves to the crypto wallet private keys of 96 users, out of a total of 6501 at the time. They went on to steal 9% of all available $PYR tokens (4.5 million PYR), leaving a loss of $135 million. Affected users have been promised reimbursement from the company’s own reserves.
Address Swapping: Malwares have been reported to swap addresses while the user is entering details of the legitimate recipient.
Flawed Multi-Sig or MPC implementations: Incorrect implementations have been leading to a single point of failure.
Security Issues of Traditional 2FACs [1]:
Issues with using SMS-Based 2FAC: SMS OTP-based 2FACs are vulnerable to a) SS7 attacks, b) SIM Swapping and c) Malwares and Trojans which trick users to provide permissions for reading messages and bypassing 2FAs.
Issues with using TOTP PIN-based 2FAC: TOTP-based authenticators have been challenged by Android Accessibility Service Mode (AAS). AAS gets permission from the user and performs critical internal interactions. As a result, an application can read or generate SMS messages, read emails, and even read Two-Factor Authentication (2FAC) codes generated by authenticator apps and record credentials entered by users on mobile banking apps.
Example attacks related to 2FACs:
Coinbase Attack 2021 by bypassing 2FAC [5]
The group (Positive Technologies) targeted a Coinbase account that was registered to a Gmail account also protected by two-factor. By exploiting known flaws in the cell network, the group was able to intercept all text messages sent to the number for a set period of time. That was enough to reset the password to the Gmail account and then take control of the Coinbase wallet. All the group needed was the name, surname, and phone number of the targeted Bitcoin user.
Badger DAO — $120 million stolen in December 2021 [6]
Hackers pilfered Bitcoin and Ethereum-based assets from dozens of user wallets, in a strategically planned attack — malicious code was injected into the platform’s website front-end almost a month in advance.
How Silent Shard was conceptualized?
The project was started by identifying common key vulnerabilities of crypto wallets. We identified that the key issues are rooted in the way private keys and seed phrases are handled, thus leading to a single point of failure. The Multi-party computation (MPC) and Threshold signature scheme (TSS). Silent Shard is based on the fusion of two approaches:
A. Decentralized Authentication using Threshold Signature Schemes (TSS) implementation of Multi-Party Computation (MPC) algorithms. The basic concept of having a private key at one place is ruled out and at no point in its life, is the private key exposed.
B. Proof ecosystem-based MFA which we call Silent Auth (holds patent/patent-pending technological contributions developed over years) for proofs of proximity, co-location, legitimate possession, liveliness via activity, identity, and other parameters.
Key Differentiators of Silent Shard:
Truly decentralized: No central custody holds any shard under its control, which substantiates the positioning of Silent Shard with high-risk cases.
Offline support: Signatures can be validated even when the nodes/devices are not online.
Private keys are never exposed, unlike solutions based on Shamir’s secret: Some of the solutions being used in the web3 security industry, as of now, are doing partially de-centralized MPC wherein private keys are exposed during each signature and shards are stored with centralized controllers like Google, LinkedIn, and other social logins. Such solutions will lead to multiple attack vectors.
Benefits of Using Silent Shard by Crypto Wallets and Exchanges
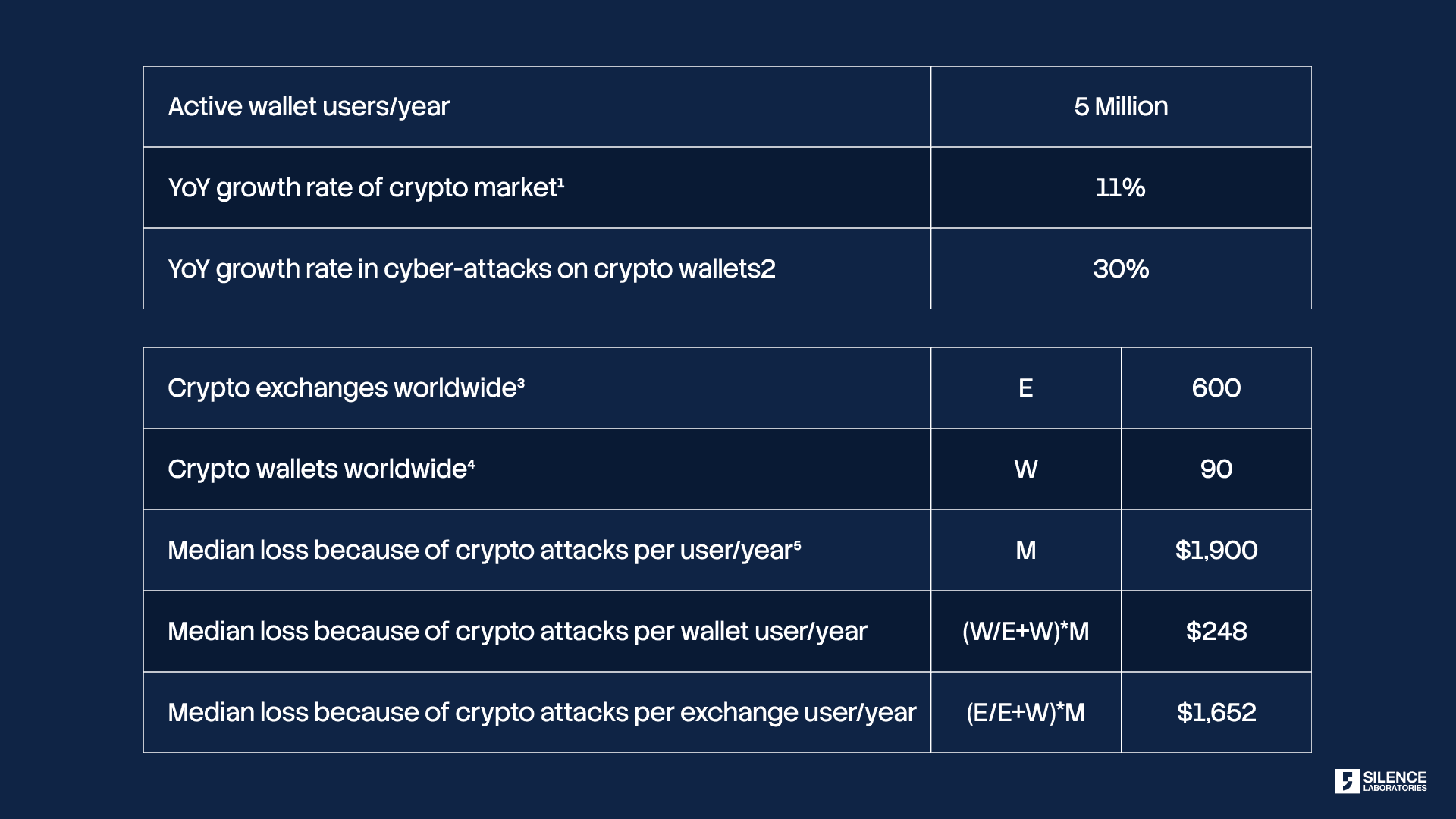
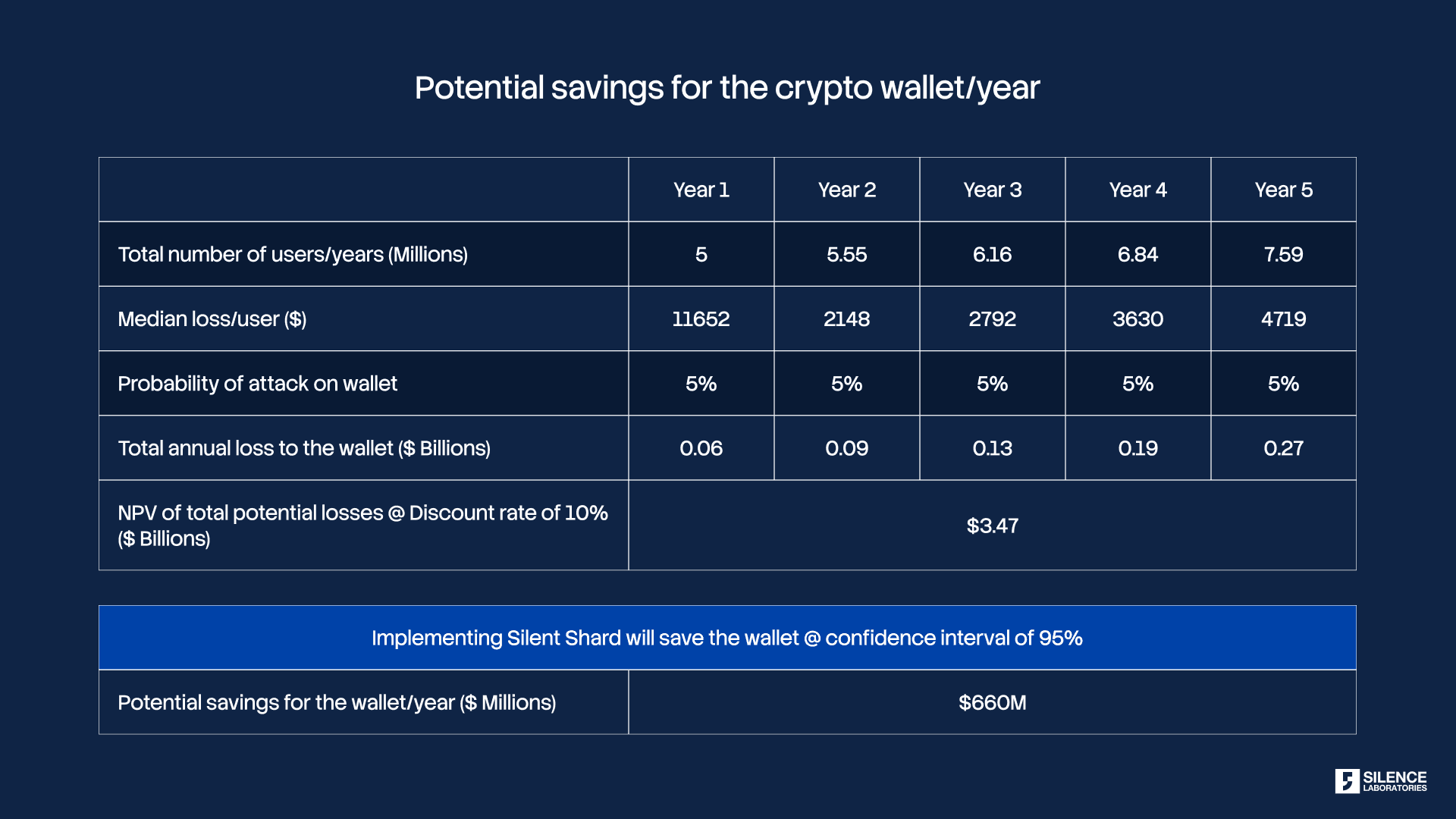
We did a thorough quantitative analysis to understand the impact of crypto attacks on Crypto Wallets and Crypto Exchanges.
Methodology: We did secondary research and encapsulated the findings with a statistical approach to identify the impact of a crypto attack on Crypto Wallet/Crypto Exchange through decision tree analysis. Following is the step-by-step procedure of the analysis:
Identification of YoY growth rate of the crypto market and YoY growth rate in cyber-attacks in the crypto world from well-published reports.
Secondary research was conducted to identify the no. of attacks in the Crypto world in recent years. Identification of median loss per user per year because of crypto attack.
Splitting the median loss for Crypto Wallets and Crypto Attacks separately through a proportional approach.
Calculation of the probability of an attack on crypto wallets/crypto exchanges based on the no. of attacks in recent years.
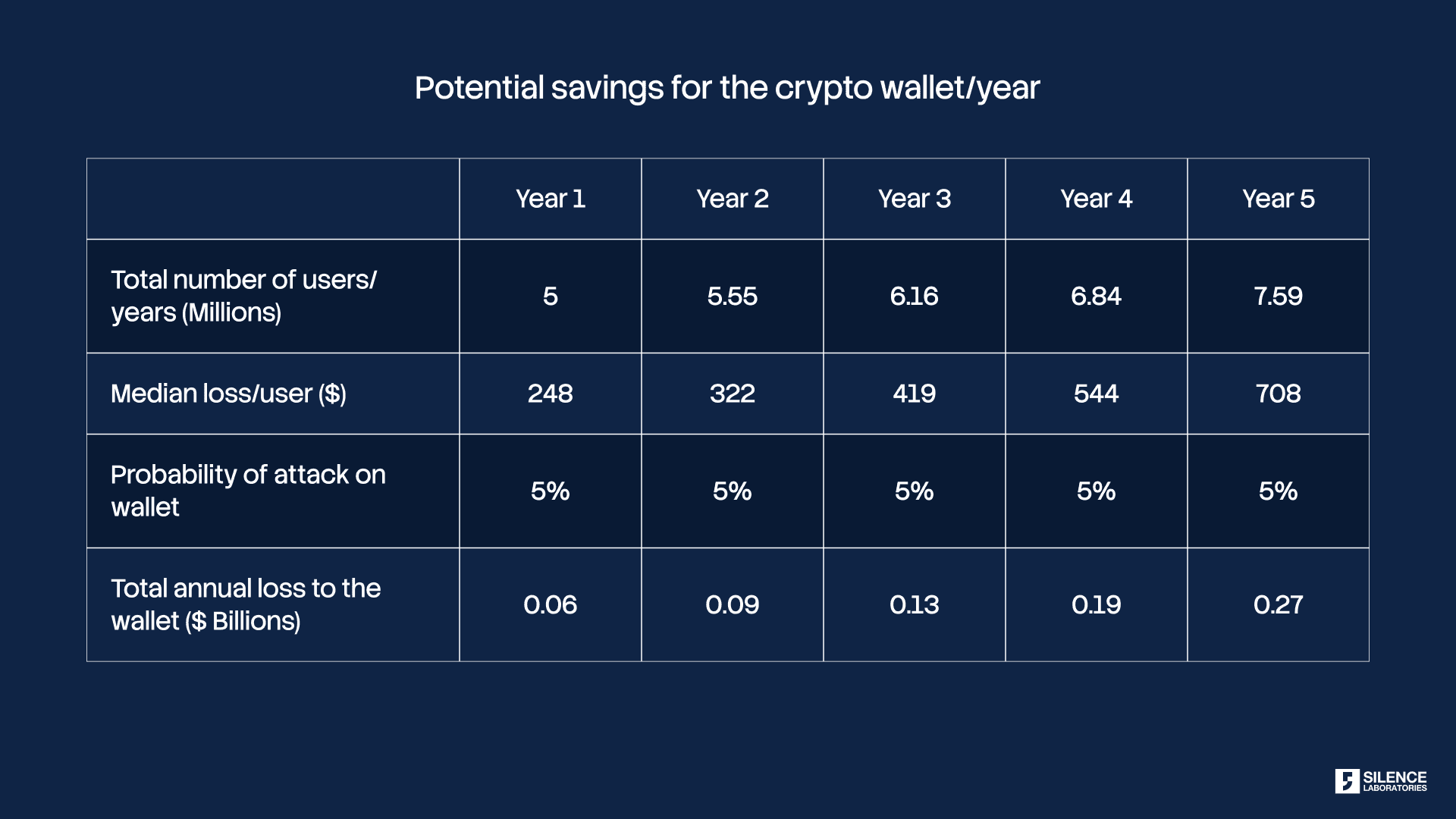
Projecting the above data over a period of 5 years to calculate the total loss for 5 years.
Taking a realistic scenario of probability for the analysis and validating it from the calculated probability in the above step.
Calculation of Net Present Value (NPV) at 10% discount rate of total potential loss for a Crypto Wallet/Crypto Exchange. It will give us the total potential loss for the wallet/exchange of 5 years. Reinforcing the 95% confidence interval of implementing Silent Shard and calculating the total loss/wallet/Year or total loss/exchange/year
Results
Potential Saving for the Crypto Wallet/Year: $ 99 million
Potential Saving for the Crypto Exchange/Year: $ 660 million
Follow the commercial benefits for a thorough analysis based on the above methodology.
1. Commercial Benefits:
Based on the data collection by Slowmist Hacked [12] there was 122 crypto attacks in 2020:
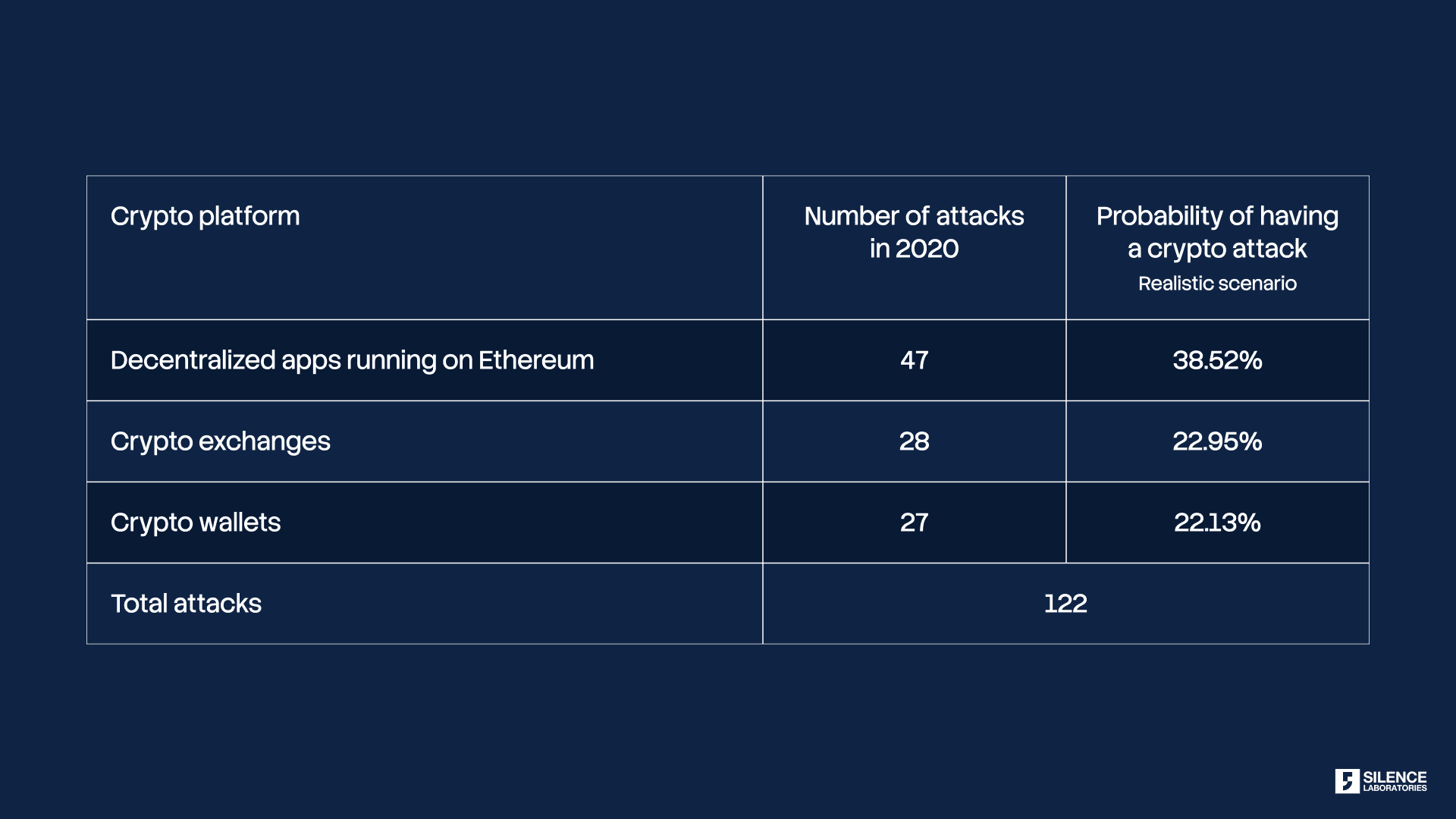
We considered a conservative scenario of having a successful attack on crypto wallet/exchange with a 5% probability for the analysis.
2. Intangible Benefits:
Enhanced Security & Usability Balance for Wallet Users
Offline support: Signatures can be validated even when the nodes/devices are not online.
A Typical User Journey with Silent Shard Authentication
A detailed documentation on architecture and user interaction points will follow in Part 2 of the blog series. Here, a brief note on one application of Silent Shard is provided.
A. Registration
During the registration (account setup process), the participating multi-parties/nodes (browser, phone, or other devices of the user) establish MPC consensus using distributed key generation. These nodes/devices can be browser local storage, a token device such as smartphones, or custom and dedicated hardware.
B. Signature
Whenever a transaction is initiated, a threshold number of the registered modalities approve the initiation of the transaction and jointly sign the transactions. The distributed signature can be facilitated either via encrypted public channels such as Amazon SQS or locally using peer-to-peer/many channels in Silent Auth, depending on the requirements of the enterprises and communities.
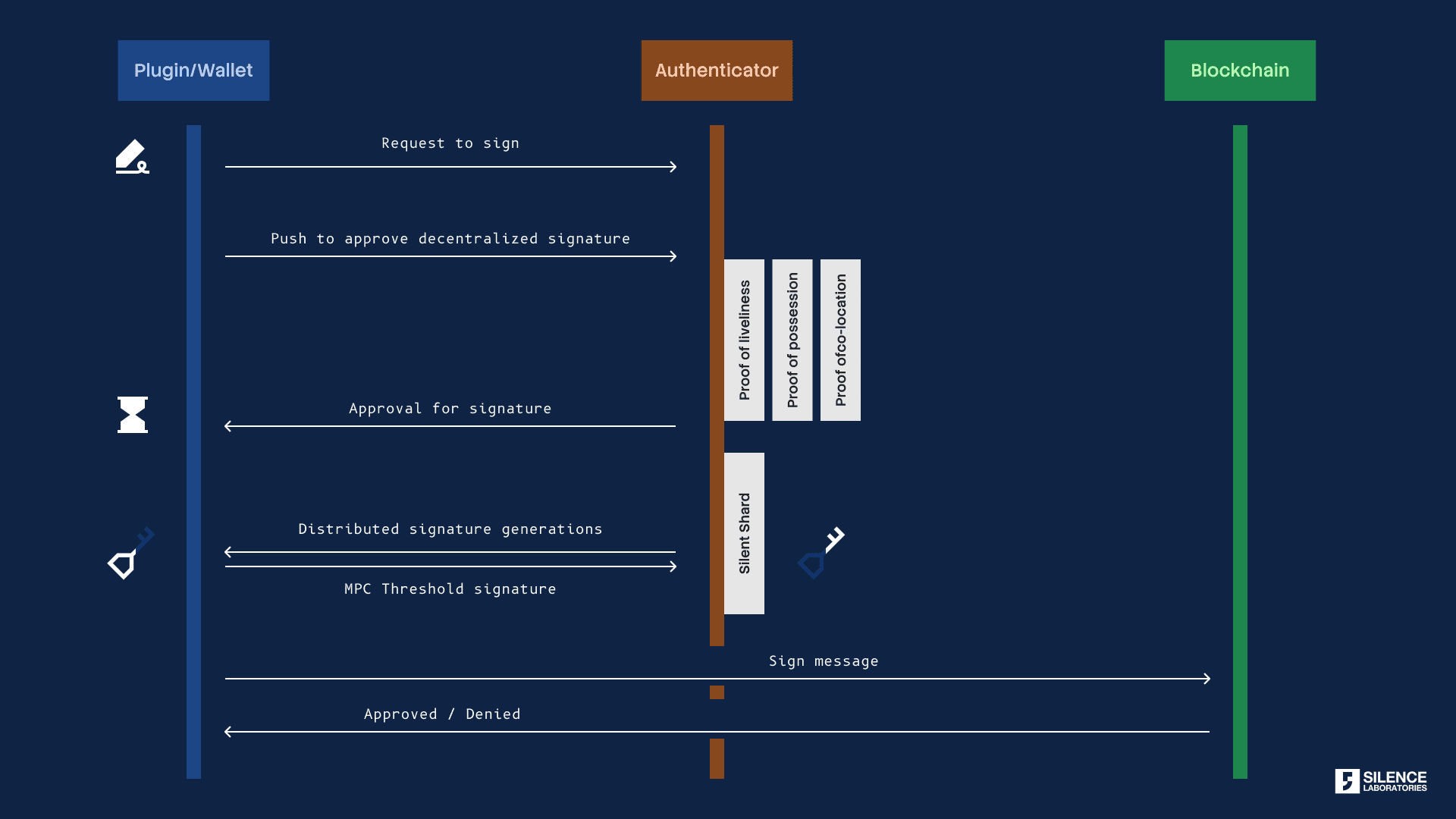
A wallet/exchange user will find it comfortable to have 2 channels to prove the possession of shards. As shown in the above figure, while the signature is validated by the verifier the protocol, off-chain proofs are needed to be validated as well. The off-chain proofs are inherent checks supported by Silent Auth which kicks multi-modal time series sensor fusion (IMUs, sound, and radiofrequency). The proofs can be defined as a function of risk. Silent Shards does check if the user who is accessing the wallet through a browser and the user which is approving a prompt to verify the signature through the registered token device, phone, are the same. It checks for the Proof of Proximity, Proof of Liveliness through the fusion of timer data and peer-to-peer communication between two participating nodes (Browser and Phone).
Our Team
Our team has a unique fusion of expertise in:
Mobile computing and security (with previous researcher affiliations at UIUC, USA & NUS, and SUTD, Singapore) and wireless communication & security (graduates from MIT, USA).
Application security and vulnerability analysis (including top ranked team in CTF).
Applied Cryptography
Wireless communication
Deep connection and understanding in Web3 community with support from Gitcoin and Kernel community.
Very strong advisory board including Prof Romit Roy Chaudhary (UIUC, USA), Prof. Jiyanying (iTrust CPS research center, Singapore), Prof. Lucienne Blessing (SUTD MIT Design Centre).
References
[1] https://silencelaboratories.medium.com/how-2fas-are-fairing-in-the-2020s-a831834ab7ab
[2] https://medium.com/easify-network/easyfi-security-incident-pre-post-mortem-33f2942016e9
[4] https://beincrypto.com/100-million-pyr-stolen-nft-marketplace-vulcan-forged/
[5] https://medium.datadriveninvestor.com/most-common-crypto-wallet-attacks-wallet-safety-cfb976e2c508
[7] https://www.fortunebusinessinsights.com/industry-reports/cryptocurrency-market-100149
[8] https://fortunly.com/statistics/cryptocurrency-statistics/#gref
[9] https://www.forbes.com/advisor/investing/cryptocurrency/best-crypto-exchanges/
[11] https://fortunly.com/statistics/cryptocurrency-statistics/#gref
[12] https://www.zdnet.com/article/billions-were-stolen-in-blockchain-hacks-in-2020/



